Cybersecurity Consultant Invoice Template
Create professional cybersecurity consultant invoices for security assessments, penetration testing, and compliance consulting. Our template includes project billing, retainer tracking, and engagement documentation. Perfect for security consultants, ethical hackers, and IT security firms. Download instantly in PDF, Word, or Excel format.
Download Popular Cybersecurity Consultant Invoice Templates
Download a ready-to-use PDF template or generate your invoice online in seconds.
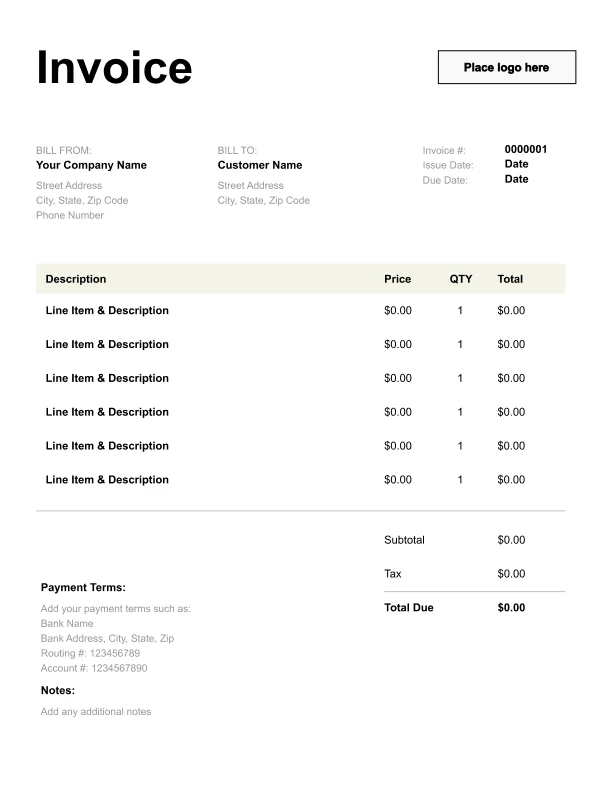
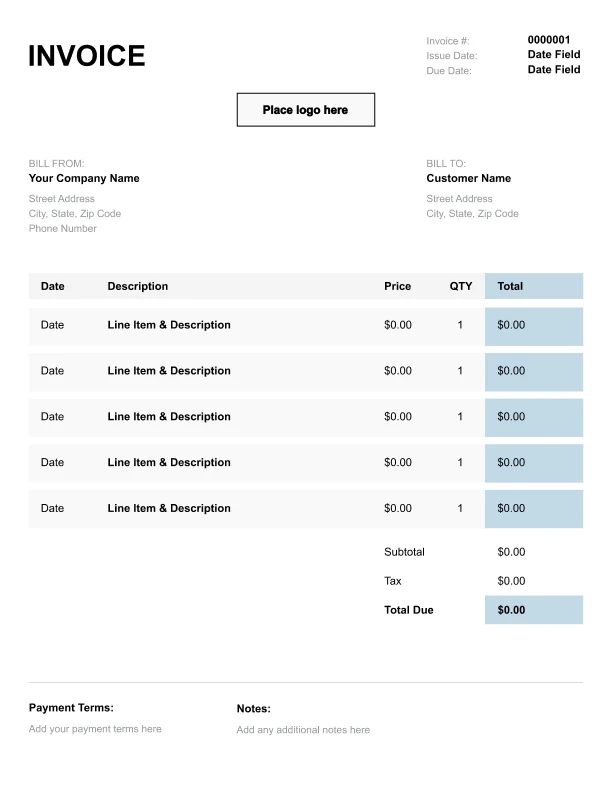
Clean Cybersecurity Consultant Invoice Template
A simple, versatile layout for services or products.
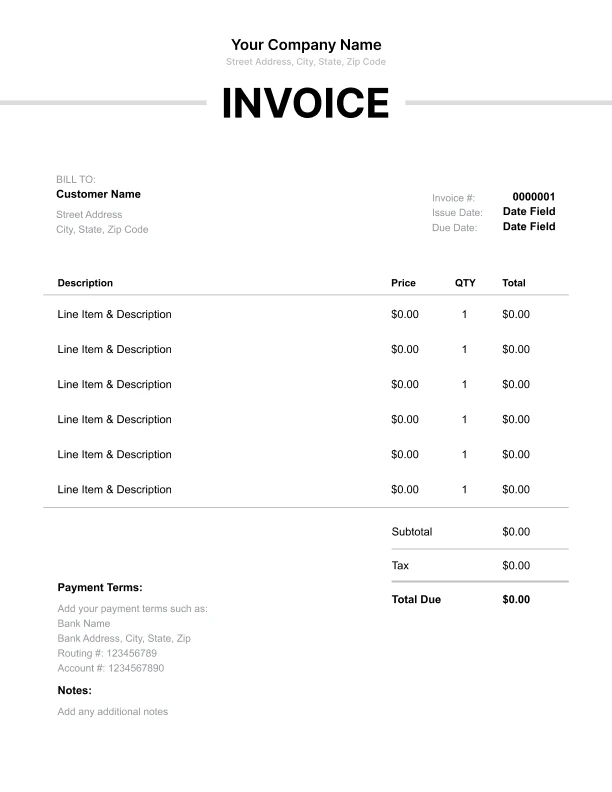
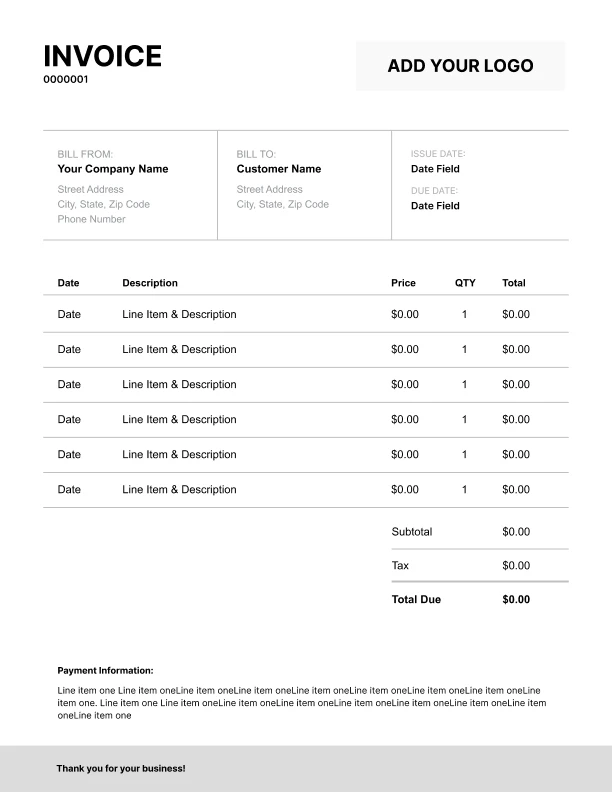
Minimal Cybersecurity Consultant Invoice Template
Lightweight design that keeps focus on line items.
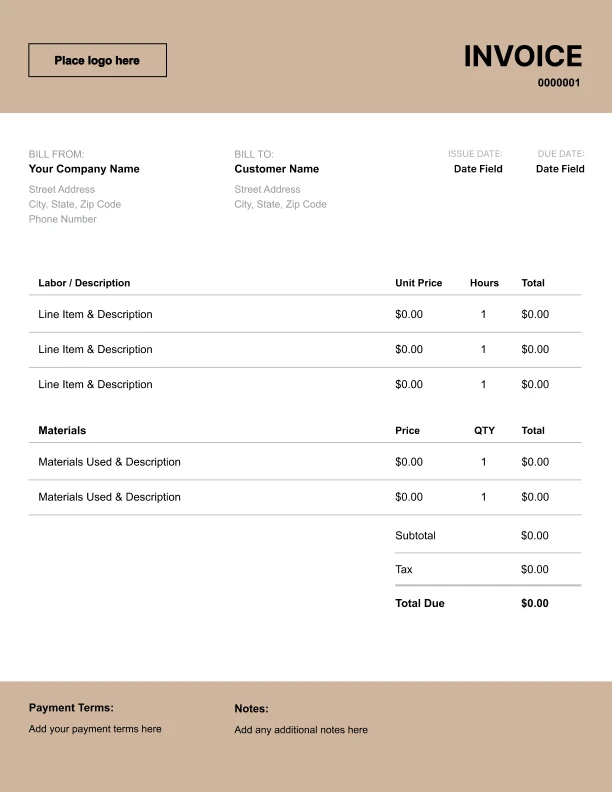
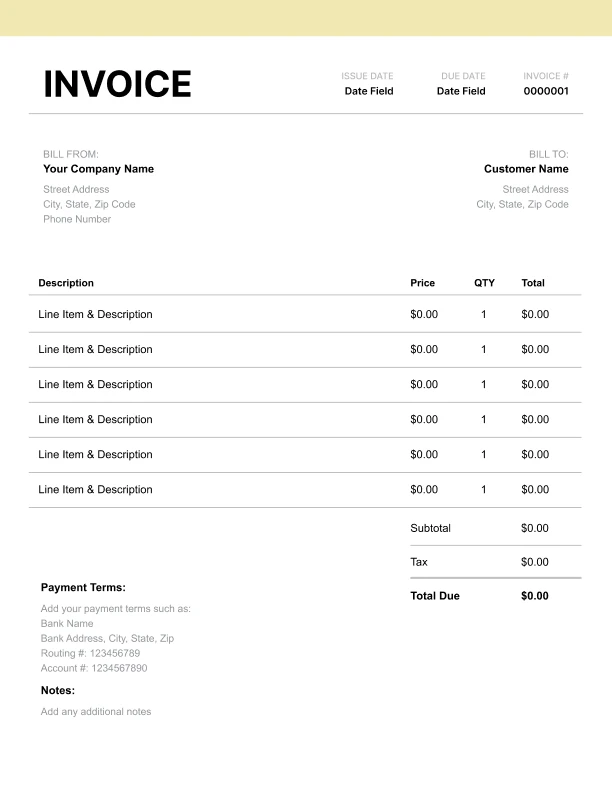
Bold Cybersecurity Consultant Invoice Template
Strong structure for large projects or milestones.
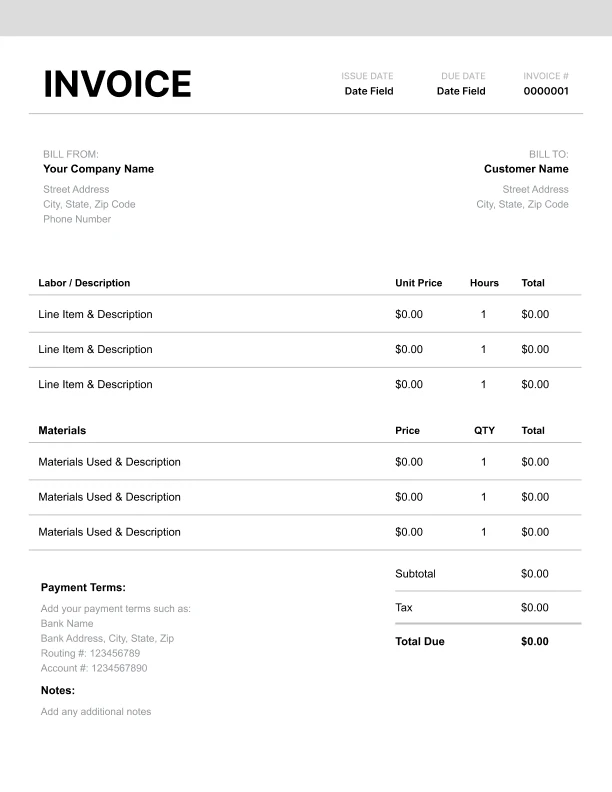
Classic Cybersecurity Consultant Invoice Template
Timeless styling that works for any industry.
Simple Cybersecurity Consultant Invoice Template
Easy to scan and perfect for quick billing.
Detailed Cybersecurity Consultant Invoice Template
Extra room for items, notes, and tax breakdowns.
Modern Cybersecurity Consultant Invoice Template
Clean sections with a subtle accent header.
Use Free Cybersecurity Consultant Invoice Generator
Prefer a polished, client-ready invoice fast? The generator auto-calculates totals, applies taxes and discounts, and lets you customize your logo and colors.
Cybersecurity Consultant Invoice Generator
What to Include on a Cybersecurity Invoice
Professional cybersecurity invoices should document:
Consultant Information- Company/consultant name
- Business address
- Email and phone
- Certifications held
- Insurance information
- Company name
- Security contact
- Billing address
- Engagement sponsor
- Project/engagement name
- Scope of work
- Systems tested
- Testing period
- Methodology used
- Assessment fees
- Testing services
- Hours by activity
- Hourly rates
- Fixed project fees
- Travel expenses
- Reports provided
- Findings severity
- Recommendations
- Remediation guidance
- Retest availability
Cybersecurity Services Pricing Guide
Standard rates for security services:
Hourly Rates- Junior analyst: $100-150/hour
- Mid-level consultant: $150-225/hour
- Senior consultant: $200-300/hour
- Principal/Expert: $275-400/hour
- CISO-level: $300-500/hour
- External network: $4,000-15,000
- Internal network: $6,000-20,000
- Web application: $5,000-25,000
- Mobile app: $8,000-20,000
- API testing: $5,000-15,000
- Social engineering: $5,000-15,000
- Vulnerability scan: $1,000-5,000
- Security audit: $5,000-25,000
- Risk assessment: $10,000-50,000
- Compliance audit: $15,000-75,000
- Architecture review: $10,000-40,000
- vCISO retainer: $5,000-15,000/month
- Managed detection: $2,000-10,000/month
- Continuous monitoring: $1,500-5,000/month
- Incident response retainer: $3,000-10,000/month
- Security training: $2,000-5,000/session
- Policy development: $5,000-20,000
- Incident response: $250-400/hour
- Expert witness: $400-600/hour
Types of Security Engagements
Common cybersecurity project structures:
Penetration Testing- Scoping and rules of engagement
- Reconnaissance
- Vulnerability identification
- Exploitation attempts
- Report and remediation
- Retest verification
- Policy and procedure review
- Technical controls audit
- Interview key personnel
- Document findings
- Risk prioritization
- Remediation roadmap
- Gap analysis
- Control mapping
- Evidence collection
- Remediation support
- Audit preparation
- Certification support
- Initial triage
- Containment
- Investigation
- Eradication
- Recovery
- Lessons learned
- Strategic planning
- Risk management
- Vendor oversight
- Board reporting
- Team leadership
- Ongoing guidance
Security Consulting Best Practices
Deliver professional security services:
Engagement Setup- Detailed scope document
- Rules of engagement
- Authorization letters
- Emergency contacts
- Out-of-scope systems
- Testing windows
- Document everything
- Maintain evidence chain
- Immediate critical alerts
- Regular status updates
- Scope change process
- Safe testing practices
- Executive summary
- Technical findings
- Severity ratings
- Proof of concept
- Remediation guidance
- Risk prioritization
- Maintain certifications
- Follow ethical guidelines
- Protect client data
- Carry insurance
- Stay current on threats
- Confidentiality always
- Clear communication
- Manage expectations
- Educational approach
- Partnership mindset
- Long-term value focus